In a presentation at the Chaos Communication Congress (Berlin, 27-30 December 2008) Alexander Sotirov, Marc Stevens and Jacob Appelbaum revealed how a weakness in the MD5 hashing algorithm could be used to create a rogue certificate.
Previous research showed the theory of this attack but this is the first practical implementation exploiting this flaw.
SSL uses server certificates to verify the identity of the server (this is the public key of the owner) and prevent man-in-the-middle attacks. When a user visits a secure (HTTPS) site the web browser retrieves the web server certificate issued by a CA (Certificate Authority). The fundamental security issue comes when a CA signs the certificate using a weak hashing function such as MD5.
Using “Chosen-prefix MD5 collisions” an attacker could manipulate a legitimate CA certificate and create a rogue one with arbitrary domain name with the same MD5 signature as the original one.
The researchers used a cluster of 200 PlayStation 3 to compute the correct MD5 hash. They used a field in the certificate called Netscape Comment Extension to inject the necessary code:
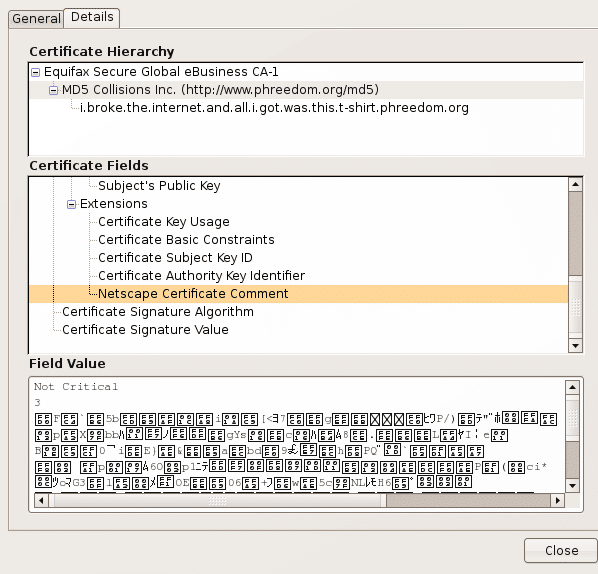
A sample of the certificate can be found in the following URL:
https://i.broke.the.internet.and.all.i.got.was.this.t-shirt.phreedom.org/
The impact of this attack is that an attacker could sign fully trusted certificates and conduct perfect man-in-the-middle attacks.
As anyone could generate this kind of certificates, revocation of known malicious certificates is not a possible option. SECFORCE recommends that the content of the Netscape Comment Extension field (and other similar fields) are checked before accepting a certificate.