What is NimWhispers?
NimWhispers is an implementation of SysWhispers2 in Nim.
Monitoring and detection
Security products such as EDR software are designed to detect potentially malicious activity running on the host. They do that by monitoring the actions performed by the user, and identifying whether those actions are potentially malicious. In order to monitor the user activities, EDR software hooks well known user-land API functions provided by the operating system.
Evasion
NimWhispers / SysWhispers are tools designed to help evasion by executing direct system calls instead of calling the user API functions provided by the Operating System.
Implant development
Threat actors pose different levels of sophistication, from script-kiddies using detectable malware to state-sponsored attackers using advanced techniques to bypass the security controls in place. Mature organisations should attempt to protect themselves from every type of threat actor, and NimWhispers helps to enhance the detection capabilities of mature blue teams.
Why use Nim for implants?
I got inspired to use Nim when I noticed the GitHub repository of byt3bl33d3r. Here are a few reasons why Nim is an excellent language for implant development:
- Firstly, Nim compiles directly to C, C++, Objective-C and Javascript. That's because it does not rely on a VM/runtime and does not produce what I like to call "T H I C C malwarez" as opposed to other languages (e.g. Golang).
- Nim has a Python-inspired syntax that allows rapid native payload creation & prototyping. It also has exceptionally mature FFI (Foreign Function Interface) capabilities.
- The language avoids making you actually write in C/C++ and subsequently avoids introducing many security issues into your software.
- It has a super easy cross-compilation to Windows from *nix/MacOS, which only requires the installation of MinGW toolchain and passing a single flag to the nim compiler.
- The Nim compiler and the generated executables support all major platforms like Windows, Linux, BSD and macOS. It can even compile to Nintendo switch, IOS & Android! (See the cross-compilation section in the Nim compiler usage guide)
- And last but not least, you can technically write your implant and c2 backend (yes, both) in Nim as you can compile your code directly to Javascript. Nim even has some initial support for WebAssembly.
For all of the above reasons, I think it is exciting to use Nim for implant development.
Why create Nimwhispers?
A repository already exists that creates syscalls using Nim: @ajpc500. Unfortunately, since it's done inline, it is largely outdated. Also a newer version of SysWhispers aptly named SysWhispersv2 was released in the meantime, which is based on the following:
- https://www.crummie5.club/freshycalls/
- https://www.mdsec.co.uk/2020/12/bypassing-user-mode-hooks-and-direct-invocation-of-system-calls-for-red-teams/
There was no public repository using the "sort by syscall" technique . Luckily, since I really enjoy creating implants with Nim, this seemed like an obvious gap to fill.
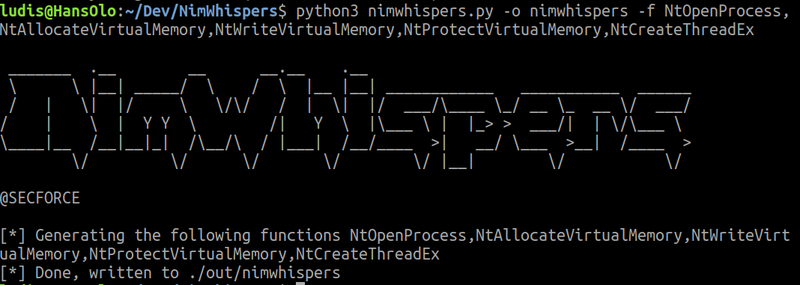
The demo
The tool works similarly to SysWhispersv2 by keeping the same command line arguments.
- To run the demo execute
nimwhispers.pywith the following arguments:
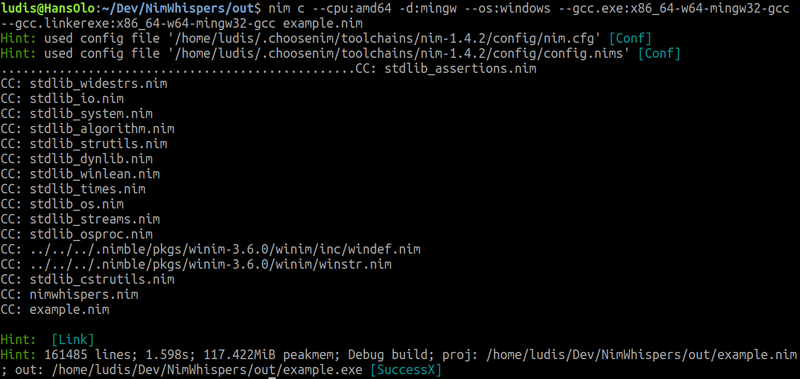
- Afterwards, compile the example code on either windows or linux.
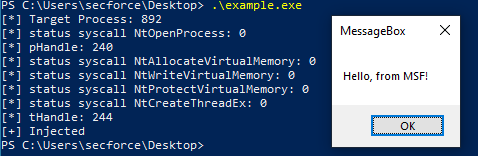
- Lastly, the output can be executed on any windows machine and call a meterpreter MessageBox shellcode.
The tool
You can download this new Nim tool at: SECFORCE's Github repository