A few days ago someone visited our website after searching in Google “why penetration test? firewall is not secure enough?”. We are going to dedicate this post just to that topic.
A firewall is a device connected to two different networks and with a number of rules which determine what traffic goes from one network to the other and vice versa. That simple. For example, a recommended configuration for a firewall protecting a web server is to filter all inbound and outbound network traffic by default, allowing only inbound traffic to your web server port (TCP/80).
Firewall protecting web server at the network layer:
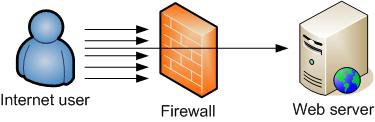
No doubts this is a good configuration which will protect the web server from many attacks. The firewall will filter network access to many services, but the question is “why penetration test? firewall is not secure enough?”. Well, the answer is no, with just a firewall the above environment is not secure enough. A firewall is always going to allow some traffic, otherwise it would be better removing the firewall and having both networks disconnected.
In the configuration above the firewall allows connectivity to the web server, therefore an attacker targeting the website will have full network access to it. The firewall will do very little to protect the web application.
So back to the question, “why penetration testing?”. Penetration testing is a method of assessing the security of a system or network by emulating a real attack scenario whereby a security consultant assumes the role of a motivated but non destructive hacker. In the scenario above a penetration test will highlight any misconfiguration on the firewall and, what it’s more important in this case, will identify any vulnerability affecting your website which could be exploited by remote attackers.
In summary, a firewall is a great security tool which can protect your infrastructure from some threats, but they certainly can not protect you from everything. Additionally, penetration testing can be beneficial to assure that your systems and applications are secure.