The Secret to Implementing a Cybersecurity Framework Easily, Quickly, and Sustainably
Published on Feb. 25, 2026 by SECFORCE
How do you successfully implement a cybersecurity framework (any framework) in an organisation?
We asked our cybersecurity consulting team, including consultants Nikos Vassakis and Kyriakos Agapaloglou, to give you the best possible answer. One key takeaway was to “see compliance as a journey (a series of processes) and not a destination (or outcome).”
But what does that mean in practice for anyone tasked with implementing a cybersecurity framework?
In a previous article, we showed you when to adopt a framework and explained how to decide between security frameworks like CIS Critical Security Controls (CIS Controls) and the ISO 27001 or implementing a large-scale project like the Secure Controls Framework (SCF) meta framework.
Now, in this article, we want to follow up and help you tackle the next step - getting real, measurable cybersecurity benefits from adopting a cybersecurity framework.
When you successfully implement a cybersecurity framework, your team will be able to link controls to outcomes and track metrics such as incident cost avoided, enterprise win rate, and audit readiness.
Here’s what you need to know to implement a cybersecurity framework in your organisation.
4 Steps to Successfully Implement a Cybersecurity Framework (Any Framework) In Your Business
Implementing a cybersecurity framework is not just figuring out what ISO 27001 (or any other framework) can do for your business (e.g., enable you to bid for certain contracts) and getting to that point. What's more important is how the framework strengthens and secures your business.
In this section, we’ll show you how to manage a cybersecurity framework implementation in a way that delivers real results.
To properly implement a cybersecurity framework, we highly recommend that companies follow these steps:
- Start with a business risk assessment and gap analysis. Then, prioritise which controls to address first based on the specific business context and constraints that apply to you.
- Build a realistic roadmap that matches your available resources. And be aware of the “planning fallacy.” Projects almost always take longer than expected, so build in extra capacity or use longer timelines than you think are needed to avoid burnout and stalled progress.
- Focus on proactive checks rather than overwhelming “problem lists.” The ease or difficulty of implementing controls will determine the next stages of your framework implementation journey.
- Integrate security into existing business operations. We explain this in more detail later in the article, but the key idea is to make compliance a natural part of your ongoing activities, not something extra you do on the side.
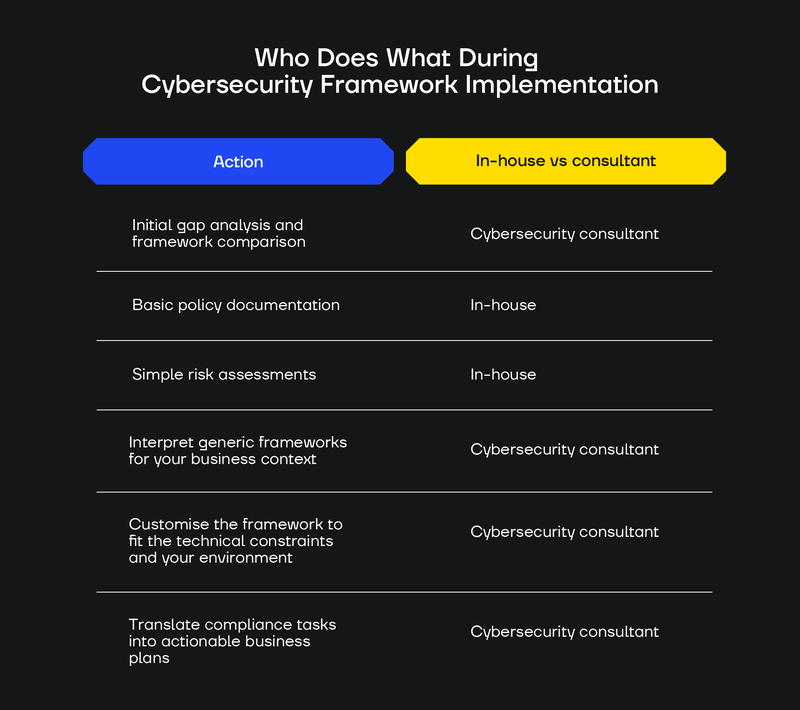
Who Does What During Cybersecurity Framework Implementation
One of the most common questions we hear from organisations considering cybersecurity framework implementation is “Can we do this by ourselves?”
The answer is “it depends.”
Most of the work involved in implementing a cybersecurity framework is done in-house by your IT, compliance, and/or security teams.
Your technical and compliance teams will also need to work hand in hand with other stakeholders in your organisation, including at the management level. All this happens with people working in your organisation.
However, some work is also best done by, or alongside, a cybersecurity consultant.
We strongly recommend starting your framework journey with a consultant to help create compliance questionnaires and the list of evidence. This will make it far more likely that you will cover all the regulations, standards, and frameworks that your organisation is obliged to comply with.
In the table below, we’ve summarised where hiring a cybersecurity consultant makes sense in the context of some of the most significant cybersecurity framework implementation challenges you will likely face.
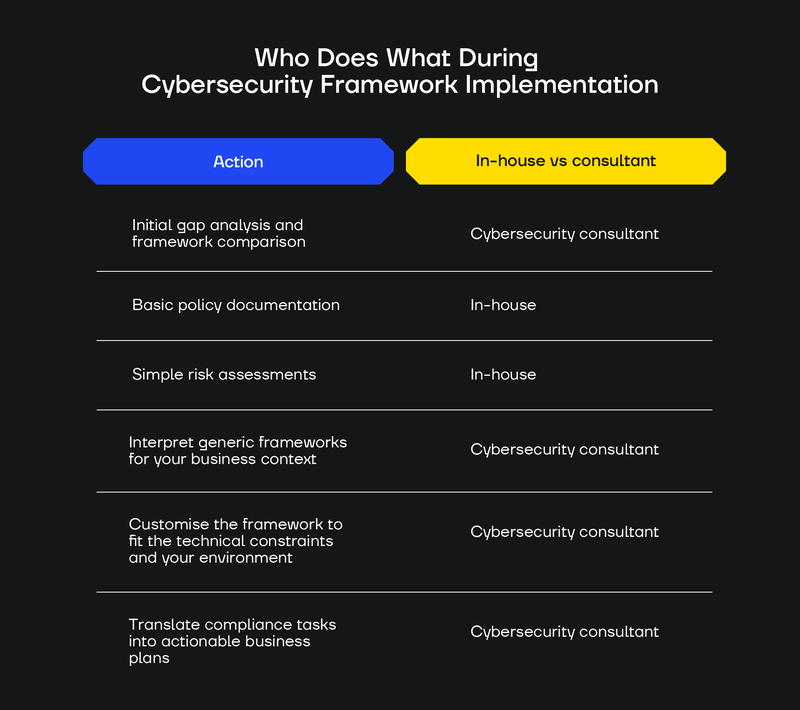
A cybersecurity consultant can also help you avoid what we call the “100 problems” trap. This is when you conduct an assessment and end up with so many issues that you have no clear idea of which problems are critical and which can be safely ignored until later on.
Consultants can customise assessments to your actual business and risk reality, helping you cut through the noise and focus on what really matters.
Security Framework Implementation ≠ "Security"
Security serves as a business enabler, not just a compliance requirement.
So, once cybersecurity framework implementation has started, long-term work begins to make it sustainable and effective.
Truly successful framework implementation, the kind that makes you more secure, is putting a process in motion. Compliance, or adherence to a framework, is the outcome, not the process.
What this means is that strong security programs:
- Integrate with business operations rather than existing as a separate security silo.
- Gradually build internal capability over time.
- Regularly review actions and implement continuous improvement processes.
Unfortunately, too many compliance and IT teams stop at documents and certificates.

Security is a living practice that must function at 3 a.m. when something breaks. Many compliant companies are hacked and suffer serious losses because they confuse compliance with security.
How to Bridge Framework Documentation And Security Work
To prevent your cybersecurity framework implementation program from becoming the kind of framework theatre we described above, we recommend treating the documentation within the framework as proof of the actions taken.
The documentation in the cybersecurity framework is evidence of a process, not the process itself.
To get real security value from a cybersecurity framework, you need to back up compliance or adherence to a framework with regular measurable actions, such as:
- Testing incident response plans with realistic scenarios.
- Ensuring policies translate to actionable, real-world procedures.
- Running targeted security awareness campaigns at specific intervals.
- Getting buy-in to clear organisational structures.
- Regular validation that documented controls actually work in practice.
Set a review cadence and keep improving. Run monthly control health checks, quarterly risk reviews, and an annual programme assessment. Capture findings in a backlog, prioritise work, close the loop with evidence, and retire controls that no longer add value.
SECFORCE can help you plan these essential cybersecurity framework implementation actions.
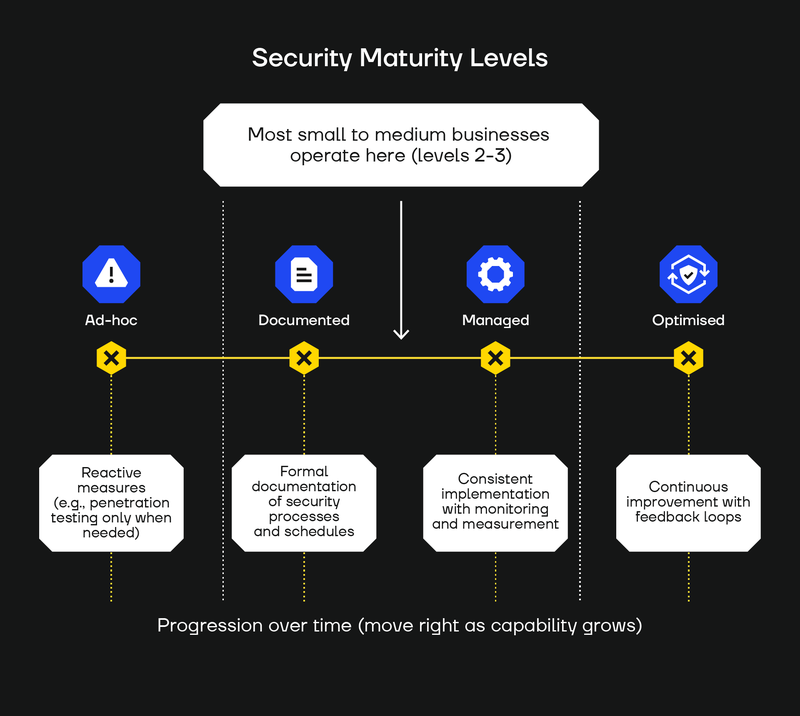
Then, use outcomes from your processes to baseline your cybersecurity maturity into Ad‑hoc, Documented, Managed, Optimised.
These help chart the next step. Our experience is that most small and mid‑size firms sit around level two or three (Documented or Managed).
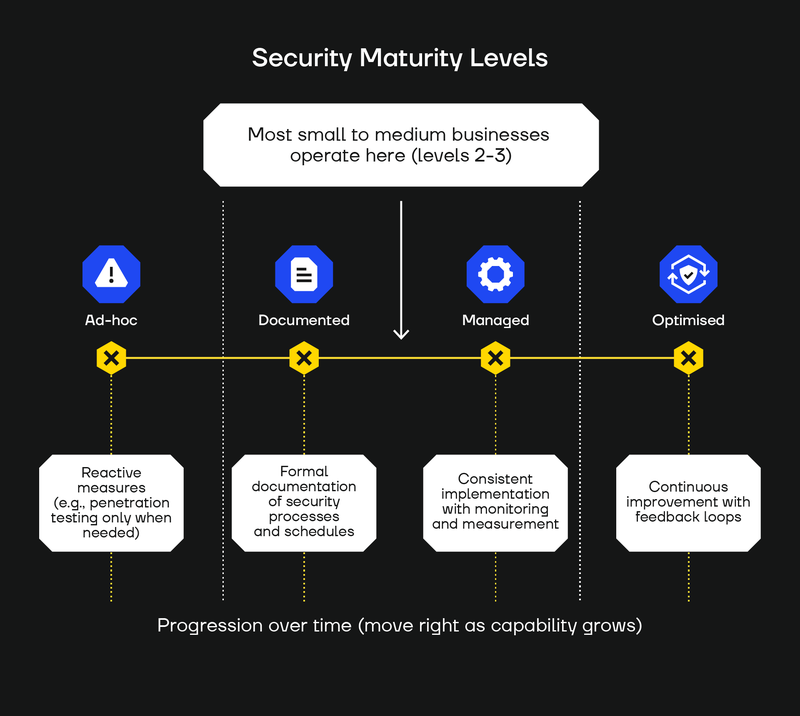
Ultimately, the only thing that moves companies forward is when paperwork turns into practice.
Your Next Steps In Cybersecurity Framework Implementation
If you are reading this and wondering where to go next, start by picking a framework that fits your needs. Match it to your sector, customer expectations, and regulatory exposure.
Your best options are likely to be the CIS Critical Security Controls, ISO 27001, or the Secure Controls Framework (SCF).
Then, compare scope, certification effort, and audit style, and choose one. Name an owner, run a quick gap review, and set a start date.
If you’re not sure which cybersecurity framework to choose, contact us for guidance and a short, tailored starter plan.
If you are already working toward adherence and want stronger security, focus on business value and risk reduction rather than ticking boxes.
A Cybersecurity Framework Consultant Like SECFORCE Can Help You
SECFORCE has been helping organisations cut through the noise and match cybersecurity frameworks to their buyers, market, and regulators for almost two decades.
Our team is here to provide you with a short gap review, a clear plan, named owners, specific dates, and a direct route to audit.
We also help you translate generic rules into controls that fit your stack and workflow, constraints included.
Our clients get a long-term roadmap with milestones, a budget, and measurable targets that keep the process moving. The payoff is durable capability, lower risk, and trust that lasts beyond any compliance check.
Contact us for a free discovery call today.
You may also be interested in...
Are Capture the Flag cybersecurity (CTF) competitions just a game? Or do they make someone better at offensive security?
See more
Our take on why a CISO might want to do Purple Teaming as one of their first actions on the job, and how Purple Teaming compares to Red Teaming.
See more