Three weeks after Jaguar Land Rover (JLR) suffered a ransomware attack, it was still unable to run any of its factories in the UK, Slovakia, Brazil, and India.
A single attack cost the brand untold millions, leading to calls for a government bailout.
From UK car companies and household name retailers, to Japanese brewers, ransomware attacks leading to business disruption are a common story for brands in 2025/2026.
The number of recorded ransomware attacks surged by 132% in Q1 2025. If you haven’t tested your ransomware protection, now is the time to do so.
More criminal gangs are entering the ransomware game, with active ransomware and extortion groups increasing by 49% year over year.
And as cybercriminals follow the money, we are seeing ransomware groups attacking anyone and everyone they think they can make a profit from. 26% of SMBs experienced ransomware attacks in the past 12 months and 23% of UK businesses have been affected by ransomware.
This article is a comprehensive guide designed to help you understand why you should test your organisation’s ransomware protection, how testing happens, and how to make the case for ransomware resilience testing in your organisation.
The Vast Majority of Companies Are Unprepared for Ransomware
We’ve helped countless organisations remediate and recover from ransomware attacks. One common thread among the most damaging incidents is overconfidence.
Companies might have great defences, backups, and recovery plans on paper, but rarely test them against current ransomware attacks from groups like LockBit, APT 29, Lazarus Group, Black Basta, and others making headlines.
Fewer still regularly test their ransomware defences as their systems and business models evolve. The data speaks for itself:
The best technology can fail, and processes fall apart when teams don’t know how it all works under fire.
The good news is that by testing your ransomware protection, you can quickly turn your organisation into a much harder target for attackers than your peers, making attacks less likely to succeed, and, if they do succeed, much easier to recover from.
The Business Case for Testing Ransomware Protection
Testing your ransomware protection delivers real business value: it dramatically reduces the risk of an unexpected operational shutdown.
Many connected and digitised businesses underestimate the extent to which their digital transformations have increased their vulnerability to ransomware-related outages. This is a core reason why more ransomware losses are coming from business disruption.
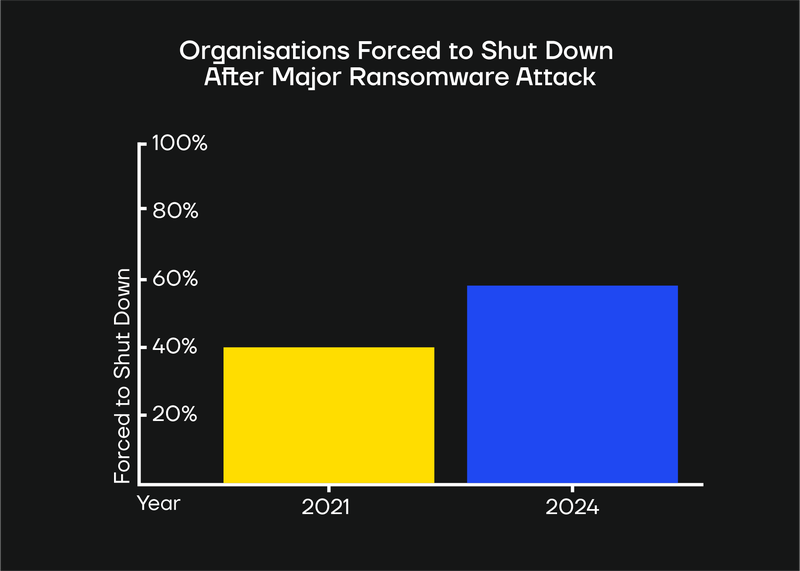
58% of organisations hit by a major ransomware attack in 2024 were forced to shut down operations to recover. This is an increase from 45% in 2021.
Making the case for ransomware protection testing in your organisation
If we were to advise a security or IT professional on how to convince management to invest in ransomware protection testing, we’d start by raising the question: How else are you answering the following questions?
- Is it possible to detect ransomware and respond quickly? Can your systems and SOC detect ransomware quickly? Can the incident be contained before it spreads?
- Are backups immutable and secure? Ensure backups are not only recoverable but also protected from ransomware tampering.
- Have supply chain and third-party dependencies been considered? Assess whether external partners (e.g., cloud providers, MSPs) are integrated into ransomware response plans.
- Is there a structure for communication and decision-making after an incident? Simulate executive, legal, and PR communications under pressure.
And if your organisation has tested their systems against a realistic ransomware scenario in the past, how have your systems changed since then? Would the results be different?
- Don’t say: We’re improving our MTTR.
- Say: We’re closing a risk that could halt our operations.
If your business stands to lose even a day of production from a successful ransomware attack, testing your ransomware defences is likely to have a positive ROI compared to the alternative.
How Ransomware Protection Testing Works
Practically speaking, the best way to test any organisation’s ransomware protection is to start with a desk-based readiness assessment and then move on to red/purple teaming, followed by gold teaming.
Ransomware readiness assessment is an audit and overview of your current capabilities.
Red/purple teaming is a realistic (but safe) test of how you would fare in a real-life ransomware attack versus real-life hackers.
Gold teaming tests how effectively leadership and key teams coordinate, make decisions, and manage communication under real-world pressure.
Below, we look at each of these in turn.
1. Conduct a ransomware readiness assessment
A ransomware readiness assessment is a structured audit of how well your organisation is prepared for a ransomware attack.
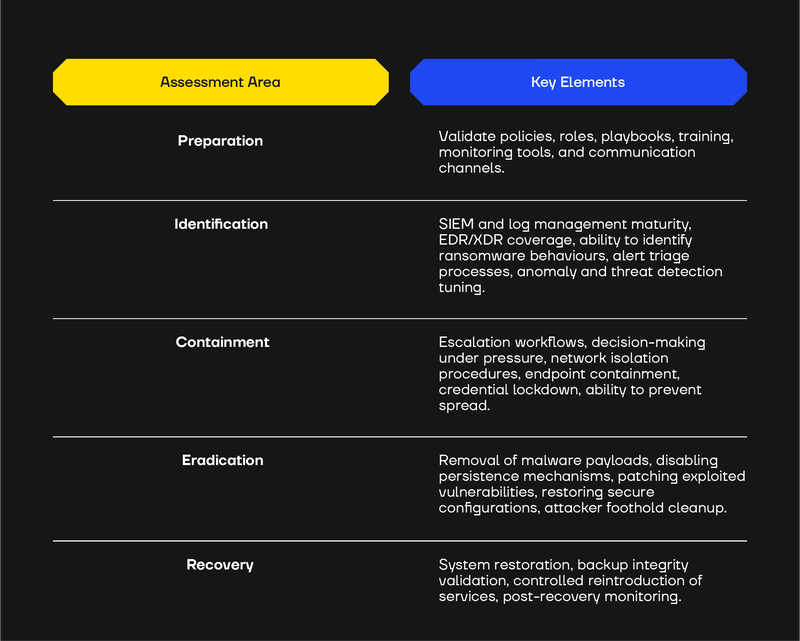
The table below outlines the key focus areas and specific elements typically examined during such an assessment.
Some companies might be able to do a portion of the work listed above internally.
If you are unsure whether your organisation is capable of conducting a ransomware readiness assessment independently, consider engaging with a cybersecurity consultancy like SECFORCE.
Why start with consulting vs. immediately testing your ransomware protection
Starting with consulting typically costs less than testing and helps you identify critical gaps before investing in more advanced validation.
If you’re missing a vital component of ransomware readiness, like a properly configured security information and event management (SIEM), endpoint detection and response (EDR), or extended detection and response (XDR) platform, it’s more cost-efficient to find this out in a consultancy engagement than during a test.
If a consultant identifies a gap, you can address it before proceeding to testing.
How a cybersecurity consultancy approaches ransomware readiness
A cybersecurity consultancy like SECFORCE starts by validating your policies, procedures, and processes.
Specifically, our goal is to help companies understand:
- What controls and policies are in place, and whether they work as intended.
- If there’s centralised logging or storing of backups. Backups being isolated (and secure against ransomware) is an important control.
- Where everything is stored (e.g., cloud?) and is it secure from ransomware.
- Gaps in key areas like those in the table above.
Based on these findings, we develop a tailored plan to strengthen your organisation’s ransomware resilience.
Adopting an “Attacker’s Mindset”
Specialised consultancies like ours take an "attacker’s mindset" approach. SECFORCE looks at your systems from the perspective of a real threat actor, seeking out the same gaps a ransomware attacker would exploit.
In longer, goal-based engagements such as red team exercises, this includes extensive internal reconnaissance. For example, looking for credentials or sensitive information stored in file shares, collaboration platforms, internal documentation systems, or developer tooling.
However, in a dedicated ransomware simulation, the objective is different. These engagements are typically shorter and focus specifically on evaluating an organisation’s ability to detect, contain, and respond to ransomware activity once an attacker already has an initial foothold.
Because of this, the testing approach is more streamlined and follows a defined sequence.
→ Initial access simulation (e.g., phishing) → Malware delivery and execution → Persistence and privilege hardening checks → Ransomware deployment simulation.
This allows us to assess how well your controls detect and respond at each stage of the ransomware kill chain.
Validating operational response and crisis communication
Ransomware readiness assessment also allows you to validate how your organisation would react under pressure in the event of a ransomware attack.
During an assessment, we help clients answer key operational questions such as:
- Would everyone know what their roles are and what actions to take?
- Are backups protected, cover all critical systems, and can you recover operations swiftly?
- Do your cold, warm, or hot sites work as intended?
- Is there a communication plan that covers internal teams, customers, partners, regulators, and the media?
Once you have completed these baseline checks and have confidence that core safeguards are in place, the next step is to test their effectiveness.
2. Test your ransomware resilience with a red team or purple team exercise
Red and purple team exercises simulate real-world adversaries using ransomware tactics, techniques, and procedures (TTPs) without exposing your business to the risks of an actual incident.
These exercises typically include a ransomware-focused malware resilience assessment and a phishing simulation, providing a comprehensive test of your organisation’s defences and response capabilities.
A red team exercise simulates a real attacker operating covertly to evade detection by the blue team. The goal is to execute an end-to-end ransomware scenario under realistic conditions, i.e., testing whether your organisation can detect, respond to, and recover from an attack without prior warning. Red teamers stay stealthy and typically begin from an external position. Learn more about our red teaming services.
A purple team exercise is a more collaborative approach. Here, offensive (red) and defensive (blue) teams work together transparently to replicate multiple attack scenarios. This allows your team to test defences, identify gaps, apply fixes, and then retest, enabling continuous improvement. Learn more about the different types of purple teaming services we offer.
Both purple and red team exercises are useful for ransomware resilience testing. A cybersecurity consultant can help you determine the best testing method for your situation.
However, we generally recommend starting with a purple team assessment to strengthen your defences, followed by a red team exercise to validate your readiness under real-world conditions.
3. Test how your organisation would react to a ransomware attack
A ransomware readiness assessment identifies how well your organisation is prepared, examining policies, controls, and processes to pinpoint strengths and gaps. Red and purple team exercises then go a step further, validating how effectively those controls and procedures perform under realistic attack conditions.
However, even with these assessments and tests in place, they don’t fully capture how your organisation would operate during an actual ransomware incident when systems are compromised, pressure is high, and business decisions carry significant consequences.
Gold team exercises fill this gap.
Building on insights from red and purple team engagements, gold teams design realistic ransomware scenarios that simulate a genuine compromise of your organisation. These scenarios are then tested through tabletop exercises involving senior leadership.
The goal is to determine whether teams can coordinate effectively, whether executive management can make timely and informed decisions, and how the organisation would manage external communication, including potential disclosure to regulators, customers, and the public.
Gold team exercises focus on testing the human and organisational response to ransomware, complementing the technical and procedural validation of earlier exercises.
A key component of these exercises is evaluating crisis communication. Having a predefined crisis communications strategy is crucial, especially for public companies. The way an organisation communicates during a cybersecurity incident can significantly influence how the event is perceived by customers, investors, regulators, and the public.
When a major incident occurs, it’s never a good idea to conceal or downplay it. News spreads quickly, and a lack of transparency often causes more harm than the attack itself. Instead, being upfront about which parts of the business were affected can help reduce confusion and prevent speculation that can impact customer trust or even stock value.
The key is to strike the right balance: provide timely and accurate updates without disclosing sensitive security details.
- Good crisis communication strategy: Acknowledge quickly, be transparent, use plain language, update regularly, tailor messages to each audience, and keep leadership visible. This preserves trust, reduces rumours, and controls the narrative.
- Bad crisis communication strategy: Delay, stay vague, go silent, give inconsistent messages, or hide leadership. This fuels confusion, speculation, and mistrust, often causing more reputational damage than the attack itself.
Gold team exercises test decision-making, cross-unit coordination, and external messaging under realistic pressure, validating your organisation's readiness so that when a real ransomware incident strikes, you can respond calmly, confidently, and credibly.
Partner with SECFORCE for Ransomware Resilience Testing
SECFORCE delivers end-to-end testing of your ransomware protection and resilience across the entire incident response lifecycle.
Our approach spans the full ransomware readiness and response cycle, from preparation to recovery and continuous improvement.
We begin by assessing your existing defences, policies, procedures, and playbooks to determine your organisation's preparedness.
We then move into active testing. Red and purple team exercises simulate real-world ransomware attacks to evaluate how effectively your detection and technical response capabilities perform under pressure.
Gold team exercises focus on leadership and coordination, testing how decisions are made and how communication flows across the organisation during a ransomware event.
Every engagement concludes with a comprehensive review of lessons learned and actionable recommendations to strengthen your controls, detection logic, and overall organisational resilience.
Contact SECFORCE today to learn more about our ransomware resilience testing services.
Ransomware Resilience Testing FAQs
Below are some of the most frequently asked questions we see about ransomware resilience testing.
What is ransomware readiness?
Ransomware readiness is about ensuring your organisation can recover quickly and confidently in the event of a ransomware incident.
Even organisations with strong detection tools can suffer severe business disruption if backups fail, recovery procedures are undocumented, or critical systems cannot be restored in a timely manner.
Ransomware readiness focuses on:
- Knowing which systems are truly critical to business continuity.
- Ensuring backups are protected, isolated, and recoverable.
- Documenting and rehearsing recovery playbooks.
- Ensuring people know what to do in high-pressure situations.
What do ransomware protection exercises include?
During an assessment of a company's ransomware protection, red and purple team exercises typically include:
Malware Resilience Testing. Attempting to deploy and execute ransomware or ransomware-like behaviours.
Phishing Exercises. Testing user awareness and email security controls.
Perimeter and Internal Testing. Evaluating both external and internal attack vectors.
How often should we test our ransomware protection?
At a minimum, conduct a full ransomware readiness assessment annually. However, you should retest whenever there are significant changes to your infrastructure, such as cloud migrations, mergers and acquisitions, major system upgrades, or after implementing new security controls.
How long does ransomware protection testing take?
The duration depends on the type of testing and the complexity of your organisation.
Contact SECFORCE for a custom, free quote.
Will ransomware testing disrupt our business operations?
No. The ransomware used by SECFORCE is coded in-house, peer-reviewed, and tailored specifically for testing scenarios.
It can encrypt specific file extensions and folders, deliver instructions to users, and display warning messages or pop-ups. It is, of course, fully reversible. That makes it both realistic and safe at the same time.
SECFORCE can simulate ransomware actions without destructive potential.
Gold team exercises are tabletop discussions that don't touch production systems at all.
Who tests ransomware protection?
Specialised consultancies like SECFORCE are available to help you test your ransomware protection.