When we asked our team of offensive security specialists what a company should do before a breach, their first piece of advice was to “make sure you understand how business continuity will be impacted by a cybersecurity breach and work backwards from there.”
If this sounds obvious to you, it is not something that the majority of companies do.
This quote from a recent article highlights the major disconnect between how people think about cyber risk and business:
"Businesses will always have a plan in case of a fire, but will not apply the same due care for a data breach – which is statistically much more likely. It flies in the face of common sense."
To help IT and security leaders understand how to mitigate cyber risks in the context of their business continuity, here are the three core actions the SECFORCE team recommends organisations take before a cyber breach.
Since 2008, SECFORCE has been helping organisations build and validate incident response plans through gold, red, and purple teaming engagements, each delivered to the highest industry standards.
1. Make an Incident Response Plan
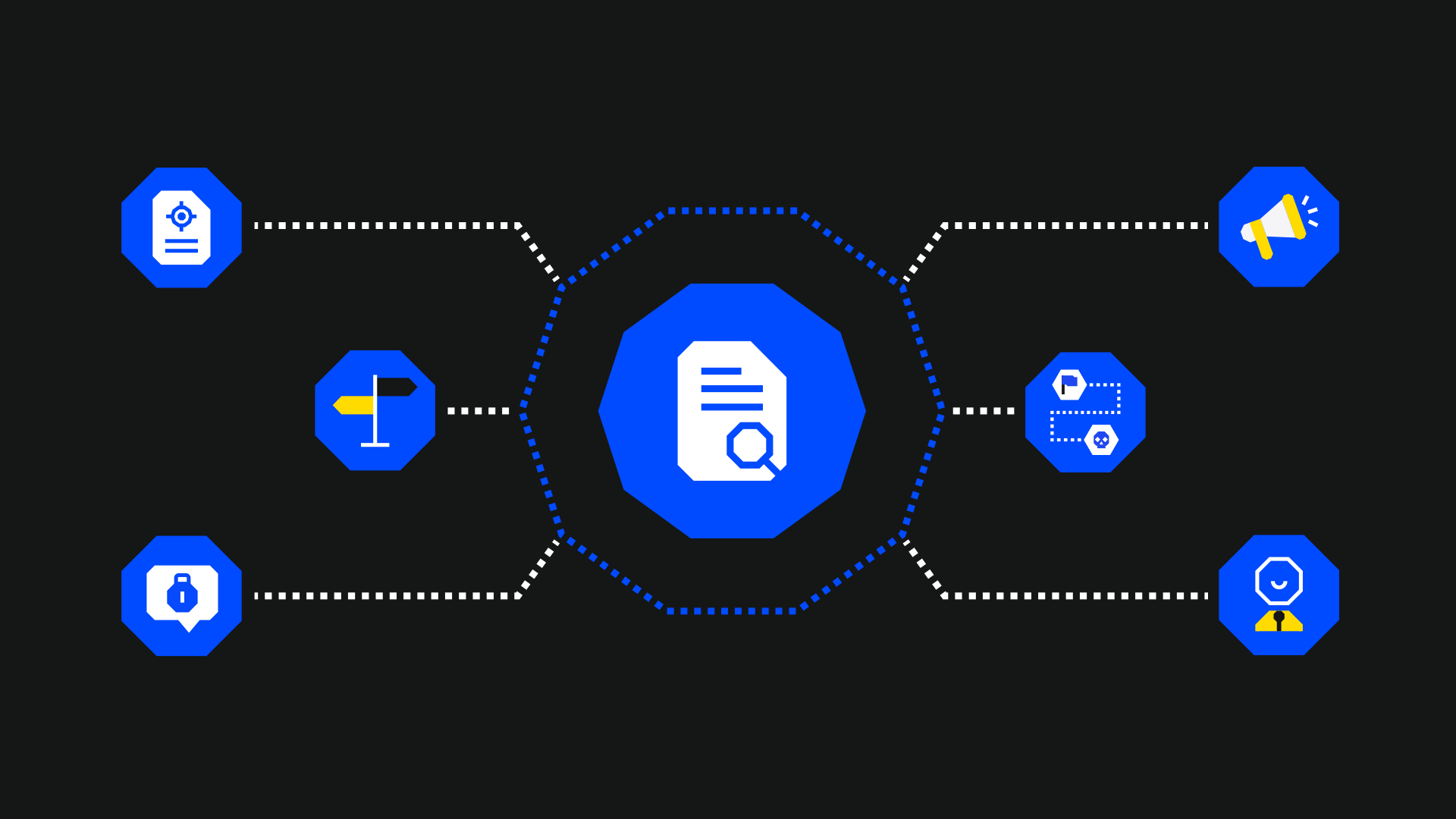
An incident response plan (IRP) is the guide to what happens after a breach, the recovery process, and who is responsible for what aspects of whatever happens next.
Unfortunately, a cybersecurity IRP is a relatively unusual thing for a business to have, but it is absolutely key to ensure a prompt recovery.
In one study, only 22% of 2,000 businesses in the UK said they have a formal incident response plan in place. That means 4 out of 5 businesses have no idea what to do in case of a cybersecurity breach.
Operating without a cybersecurity IRP is dangerous
Creating and testing a cyber IRP might be one of the best things you can do to safeguard your organisation (and your career) this year.
Specifically, a cybersecurity IRP will lay out:
- Who is responsible for what when a breach happens, e.g., who reports to the regulator, who takes charge of remediation, who talks to the press, etc.
- Clear communication channels and protocols for all the different stakeholders involved.
- Escalation processes for different types of incidents and what happens in various risk scenarios.
Your IRP may differ, but the outcome will be the same
The specifics of any IRP will vary from company to company.
For example, for financial services entities subject to the Digital Operational Resilience Act (DORA), there needs to be a dedicated procedure for meeting DORA reporting and information-sharing requirements.
However, for every organisation, the goal is to minimise recovery time (RTO/RPO) by creating an incident response & disaster recovery plan and a clear map of critical assets.
An incident response & disaster recovery plan is a solid plan before a crisis occurs about how to bring back services or mitigate data loss. Knowing exactly who to call and what to do reduces chaos after a breach is noticed or a system goes offline.
A clear map of critical assets provides the assurance that essential systems can be rapidly accessed, assessed, and recovered in any likely threat breach scenario.
To put it another way: Proactive planning means you won’t have to deal with chaotic reactions.
Your IRP will heavily rely on your BCP (Business Continuity Plan)
You need to have a protocol to follow after a breach, i.e., an incident response plan (IRP)
However, you can’t plan for what to do after a breach without a Business Continuity Plan (BCP).
The BCP is where the critical functions and information assets in the organisation are identified, and security measures are implemented to protect them, such as back up policies, redundancy of systems, anti tampering mechanisms, log storage, etc.
Without a BCP you cannot create an IRP.
2. Test Your IRP Before a Cyber Breach with Tabletop Exercise (Gold Teaming)
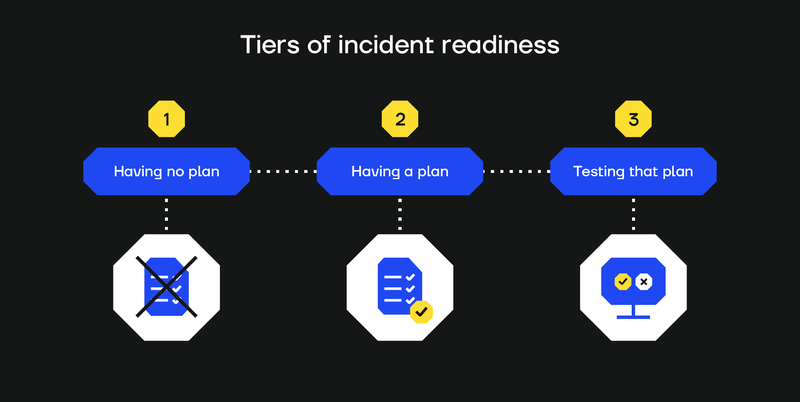
Out of 10 organisations, 2 or 3 might have a response plan, but how many will test and update it on a periodic basis?
In our experience, the percentage of companies with tried and tested IRP is dangerously small. Few organisations make enough effort to test and refine their cybersecurity IRP once it has been drawn up.
Don't wait for a breach to test your IRP
Most organisations only figure out what's missing or poorly covered in their plan when a breach actually happens.
The tried and tested way to improve and test an IRP (before a breach does it for you) is to conduct purple teaming and gold teaming exercises (i.e., tabletop exercise).
Purple teaming is a live collaboration between “hackers” and your blue team to find and fix holes in your detection and response processes in real time.
Gold teaming is a testing method that brings tech and non-tech managers into a simulated crisis, such as a ransomware attack, to evaluate how different teams respond. This includes going through the escalation process, testing communication and recovery procedures, identifying gaps across all response stages, and more. You can read more about gold teaming here.
3. Test the Corrective and Preventive Controls That Underpin Processes
A high-level plan, even when tested at a theoretical level, is no good if no one also practically tests whether the controls and processes mentioned in that plan are effective or even exist in reality.
Don’t blindly trust your plan
An organisation might have well-documented incident response protocols that detail how backups will be used to restore systems in case of encryption.
Their IT or security leadership might also test how they would react at an organisational level using tabletop exercises like gold teaming.
But that same organisation could still discover during a ransomware attack that all their backups have been encrypted. When no one in an organisation takes the time to test that the segregation of backups has been done properly, this kind of scenario can happen.
Backups and other measures also need to be aligned with recovery priorities. A sequence for restoring systems is crucial, especially in complex environments with redundant or replicated systems.
Test your detection and response solutions
The same goes for preventative controls like endpoint detection and response (EDR) or antivirus (AV) solutions that might theoretically detect certain kinds of tactics, techniques, and procedures (TTPs) and help contain incidents, but may not always do so in reality.
For instance, it's a well-known fact that at least 44% of commonly used SIEM rules are likely to be redundant or easily evaded.
These kinds of tools need to be assessed in your operational context.
However, the most important technical capability our team recommends focusing on is the ability to test telemetry. Telemetry is an organisation’s ability to collect, transmit, and measure data related to IT events.
It's essential to test your baseline telemetry before a breach to make sure you have the ability to accurately detect the presence of an attacker or compromised systems after a breach happens.
Telemetry is critical
Test your telemetry and the effectiveness of your security controls before a breach with purple teaming and/or red teaming:
Purple teaming can test detection rulesets and give your blue team real telemetry to show you what is working well and what isn't.
Red teaming before a breach simulates real-world attacks in particular areas of your environment to show real-world paths to compromise that would otherwise be missed in theoretical planning or more limited testing.
If a red team is detected, the test can sometimes turn into a purple team (if the tested organisation wants to). This is in order to continue the test and cover the scenarios agreed.
In this case, the level of access prior to detection is restored (leg up), and the read team continues the test. The blue team knows a test is taking place, and information about the attacks is shared between the teams.
Purple teaming is especially useful when you’re:
- Configuring detections for the first time (the initial setup phase).
- Preparing for a red team exercise.
- Taking a broad approach that aims to cover as many attack vectors as possible.
- Training internally or working within a smaller budget.
However, for most other scenarios, a red team will give you the same benefits as a purple teaming exercise. After all, a red teaming exercise can become a purple teaming exercise.
Testing and improving telemetry enhances your ability to see and contain malicious activity before a breach and will make an immense difference to your recovery after a breach.
Bringing Everything Together Before a Breach
Preparing a strong defence is key to recovery, but preparation cannot be a single exercise or a copy-and-paste template.
The likelihood of any given organisation experiencing a significant breach in an average year is now very high (1 in 4, according to some sources). But by rehearsing your incident responses, updating plans, and assessing security controls, there is no reason why any security incident you are likely to face should seriously impact your business continuity.