SECFORCE’s Guide to Building Cyber Resilience. What Does It Really Mean to Be Cyber Resilient?
Published on May 6, 2026 by SECFORCE
To be cyber resilient is to sleep well at night.
IT teams in cyber-resilient organisations know they have done most of the work needed to anticipate, withstand, and recover from IT incidents. With well-tested defences and response plans in place, no one is secretly stressed about getting a call at 2 am or the chaos that would come after a cyber incident is discovered.
But most organisations do not feel this confidence in their resilience efforts. So what should they do to become more cyber-resilient? The short answer is testing.
For almost 20 years, SECFORCE has provided offensive security testing services to build cyber resilience, including CREST-accredited penetration testing, red and purple teaming, and gold teaming exercises that strengthen prevention, detection, and recovery capabilities.
This article is a condensed version of the advice we might give to clients who want to understand and improve their cyber resilience.
It’s based on our team’s extensive experience helping clients make their environments more cyber resilient from a variety of starting points.
Resilience Is Built On Prevention, Detection and Recovery
In our experience, resilience is built on three pillars:
- Prevention.
- Detection.
- Recovery.
Here’s what each means in practice and how offensive security testing can help you build each one.
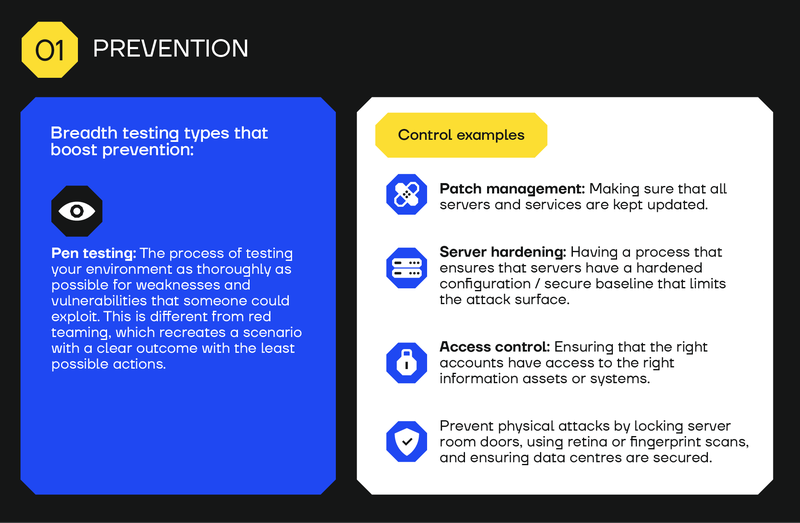
Prevention - Improving prevention through penetration testing and deployment of security controls
Prevention is the process of making it difficult for cyber incidents to occur in the first place.
It means implementing the necessary security controls and testing to ensure they are working effectively, at least for the systems and services critical to the business.
This can be called "breadth testing," i.e., using testing methods that test all your critical systems for weaknesses. This is in contrast to red team engagements, which are “depth testing,” i.e., going after a target system.
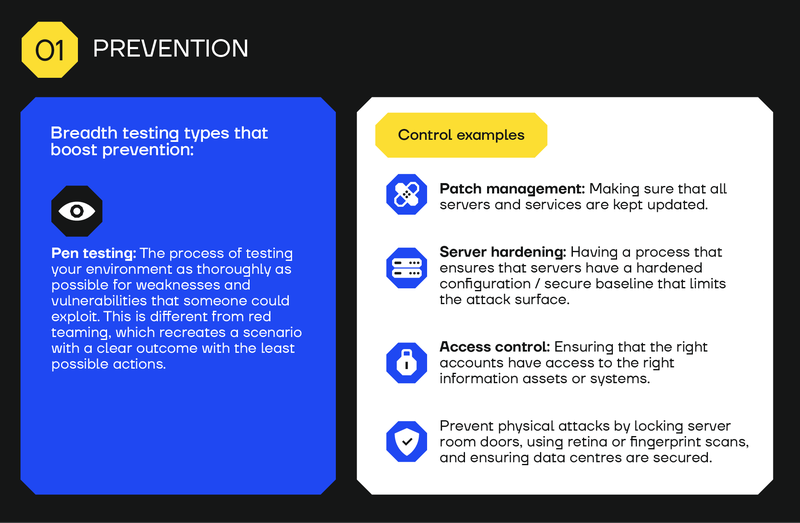
Breadth testing types that boost prevention:
- Pen testing. The process of testing your environment as thoroughly as possible for weaknesses and vulnerabilities that someone could exploit. This is different from red teaming, which recreates a scenario with a clear outcome with the least possible actions.
Control examples:
- Patch management: Making sure that all servers and services are kept updated.
- Server hardening: Having a process that ensures that servers have a hardened configuration / secure baseline that limits the attack surface.
- Access control: Ensuring that the right accounts have access to the right information assets or systems.
- Prevent physical attacks by locking server room doors, using retina or fingerprint scans, and ensuring data centres are secured.
Benefits of pen testing for cyber resilience
Pen testing finds exploitable vulnerabilities, allowing you to fix them before attackers find them.
Finding and fixing exploitable vulnerabilities can make a massive difference to your organisation’s cyber resilience. A robust penetration testing programme, which assesses the security controls of critical systems, understands the risks of the organisation holistically, simulates realistic scenarios and is followed by timely remediation, is the first step towards effective prevention.
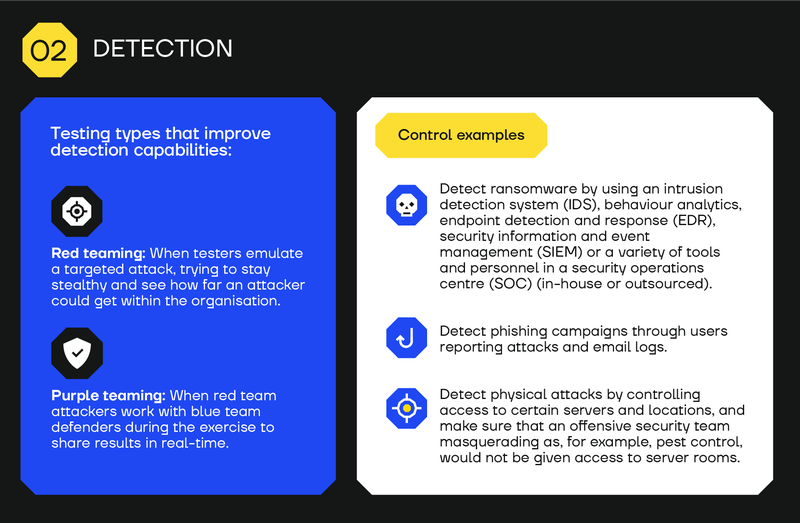
Detection - Testing your detection capabilities with a red team engagement
No combination of security controls can be relied on to work 100% of the time. Resilience means being able to detect ongoing incidents as early as possible.
That’s why resilient organisations use red teaming and purple teaming to test their monitoring functions and stay ahead of evolving threats.
Red teaming is beneficial in a number of areas, but due to its very realistic nature, it becomes a powerful tool for assessing how effective the existing SOC team is at identifying realistic attacks, performing triage, and reacting to them effectively.
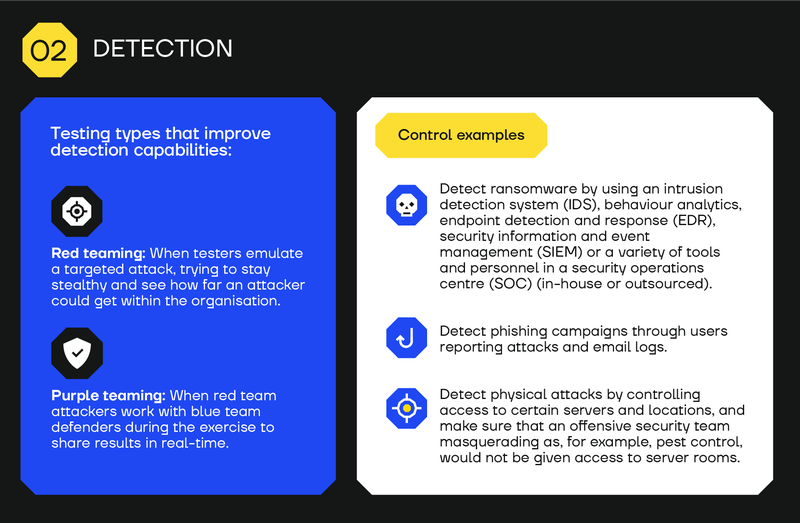
Testing types that improve detection capabilities:
- Red teaming. When testers emulate a targeted attack, trying to stay stealthy and see how far an attacker could get within the organisation.
- Purple teaming. When red team attackers work with blue team defenders during the exercise to share results in real-time.
Control examples:
- Detect ransomware by using an intrusion detection system (IDS), behaviour analytics, endpoint detection and response (EDR), security information and event management (SIEM) or a variety of tools and personnel in a security operations centre (SOC) (in-house or outsourced).
- Detect phishing campaigns through users reporting attacks and email logs.
- Detect physical attacks by controlling access to certain servers and locations, and make sure that an offensive security team masquerading as, for example, pest control, would not be given access to server rooms.
Benefits of red teaming and purple teaming for cyber resilience
Even with the latest and greatest detection tools, the people monitoring your organisation’s network need to be able to identify and classify an attack against a false positive alert.
Emulating an attacker in a red team exercise helps understand how well detection software (e.g., AV, EPP, EDR, or another tool) works and where it falls short.
Red teaming can also help you understand how attackers would operate within your organisation’s network, e.g., where they could move to, what assets they could exfiltrate, which users are vulnerable, etc.
Red teaming trains your team to be able to identify attack patterns.
Purple teaming is similar.
Like red teaming, purple teaming helps configure an organisation's detection capabilities.
Unlike red teaming, purple teaming is a more open-book, collaborative exercise between the two teams (red and blue) and therefore less realistic in nature.
However, purple teaming also helps the blue team see how attacks are identified in their network and what kind of alerts to expect for the different types of attacks.
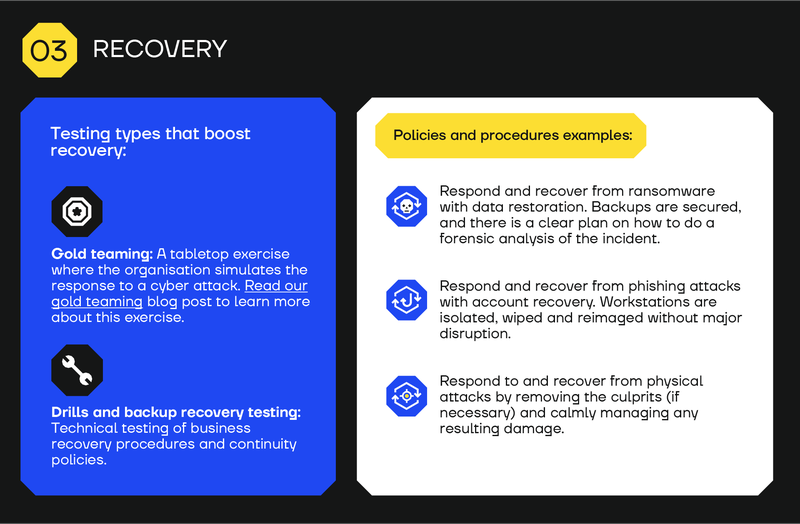
Recovery - Testing incident response by gold teaming and testing recovery/continuity capabilities
A resilient organisation knows exactly what to do when an incident is detected and how recovery will take place.
Everything has been planned and tested. For example, which teams are responsible for finding and containing damage, how many days they can withstand an attack while still running the business, who will talk to regulators and the press, etc.
Response and recovery processes are clearly mapped out and tested at the technical and executive levels through technical testing of recovery procedures and continuity policies, e.g., drills, backup recovery testing, and gold teaming (which brings in non-security stakeholders).
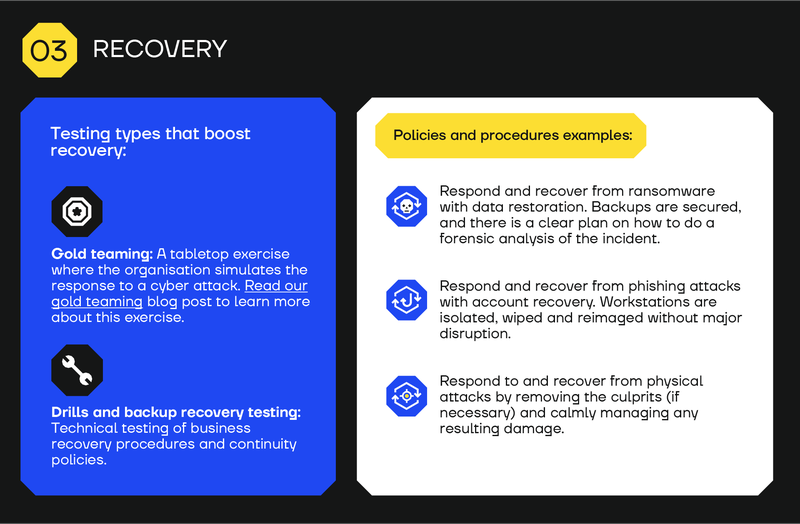
Testing types that boost recovery:
- Gold teaming. A tabletop exercise where the organisation simulates the response to a cyber attack. Read our gold teaming blog post to learn more about this exercise.
- Drills and backup recovery testing. Technical testing of business recovery procedures and continuity policies.
Policies and procedures examples:
- Respond and recover from ransomware with data restoration. Backups are secured, and there is a clear plan on how to do a forensic analysis of the incident.
- Respond and recover from phishing attacks with account recovery. Workstations are isolated, wiped and reimaged without major disruption.
- Respond to and recover from physical attacks by removing the culprits (if necessary) and calmly managing any resulting damage.
Benefits of gold teaming for cyber resilience
How do you know you have an actionable, clear plan and the right people and procedures for when a security incident happens?
Answer: You make a plan and test it.
Gold teaming gives you a preview of what would happen in the event of an incident. Not just in technical terms, like with pen testing and red/purple teaming, but to the actual business. How will you tell the world, deal with downtime, and what happens next.
That’s why gold teaming is probably the best way to bring cyber resilience planning beyond IT silos.
Cyber Resilience Is a Business Asset
Aligning cybersecurity to business continuity through resilience is one of the best ICT investments an organisation can make.
According to Accenture, organisations that build cyber resilience like this are 18% more likely to increase their ability to drive revenue growth, increase market share, and improve customer satisfaction, trust, and employee productivity.
Resilience also saves money by reducing the potential cost of experiencing a cyber attack and protects against the significant reputational damage that a poorly managed cyberattack can cause. A study of fintech leaders found that 78% ranked reputational damage from a cyber incident as their top concern.
Testing Is How You Build True Cyber Resilience
A famous military saying is that “no plan survives first contact with the enemy.” The same is true for cybersecurity.
The best way to boost cyber resilience is to simulate attacks in a controlled manner. That way, an organisation can understand exactly where their security plans work and where they do not.
Testing helps build cyber resilience through continuous improvement.
By using testing to boost cyber resilience, an organisation can:
- Find weaknesses and vulnerabilities before an attacker does.
- Understand attacks as they happen.
- Understand how well their defensive controls and processes work.
- Get telemetry from events.
- Prepare their SOC and blue teams.
In other words, they can gain the confidence that they are resilient and can withstand attacks.
Get More Resilient with SECFORCE
SECFORCE’s primary objective is to help clients build cyber resilience.
The testing methodologies we use vary depending on a company’s circumstances, but the goal is always the same: to make our clients more resilient against ICT incidents.
If you want to understand, build, or improve your organisation's cyber resilience, ask us about our cyber resilience services.
Contact us today.
You may also be interested in...
What does a red teamer actually do in real life? To give you the full story and a realistic look at what it means to be a red teamer, we asked a full-time SECFORCE red teamer about his day-to-day job.
See more
In this blog post, we give you a behind-the-scenes look at pen test pricing in 2026 and share an 11-point checklist for UK and EU pen test buyers.
See more