If you are responsible for greenlighting security spending requests (or are talking to someone who is), you might want to keep one concept in mind:
Proactive security is always cheaper than reactive security.
We recognise that claiming one security spending approach is always cheaper (and better) than another is a significant assertion to make.
However, having helped hundreds of companies recover from various types of cyber incidents, we can assure you that cybersecurity incidents are almost always more damaging and expensive than companies anticipate.
Research backs us up, too. According to IBM's Cost of a Data Breach Report 2025, the average cost of a data breach in the UK is approximately £3.11 million ($4.14 million).
SECFORCE has over 18 years experience providing proactive security testing services, including CREST-accredited penetration testing.
We often see a disconnect between the real costs of far-away risks (such as a potential ransomware attack) and the present-day costs of cybersecurity might be part of the reason why the majority of companies spend less than the recommended (but already small) 10% of their IT budget on security.
This blog post was written to give realistic information to IT and security leaders when it comes to justifying the investment in proactive cybersecurity.
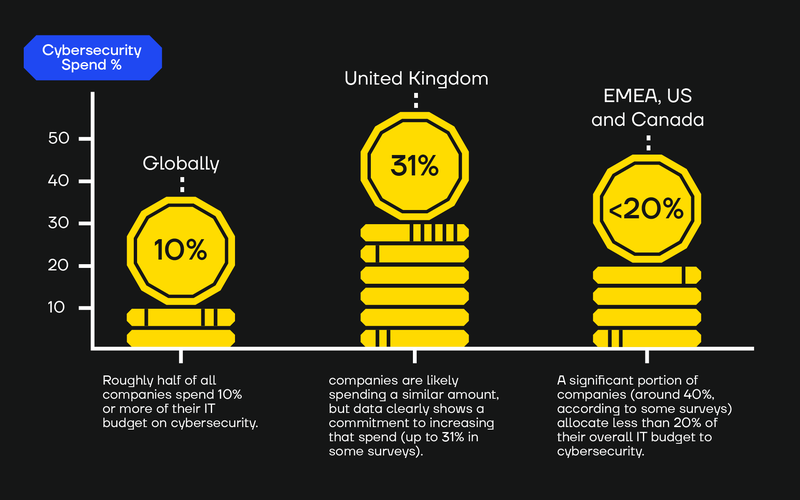
How Much Are Companies Spending on Cybersecurity?
Around 1% to 2% of a company's total annual budget is allocated to cybersecurity, according to the latest data on cybersecurity spending.
- Globally: Roughly half of all companies spend 10% or more of their IT budget on cybersecurity.
- In the United Kingdom, companies are likely spending a similar amount, but data clearly shows a commitment to increasing that spend (up to 31% in some surveys).
- Across the EMEA, the US, and Canada: A significant portion of companies (around 40%, according to some surveys) allocate less than 20% of their overall IT budget to cybersecurity.
To summarise this cybersecurity spending data: A company operating in a developed country, such as the UK, the US, or any EU member state, is likely to allocate 10–20% of its IT budget to cybersecurity. That said, research shows that organisations globally are increasing their cybersecurity budgets.
Why Is Cybersecurity Spending On the Rise?
This trend of increased cybersecurity expenditure aligns with accurate and effective risk management in mature organisations, which understand the value of their information assets, their reliance on technology, market perceptions of their reputation, and the cost of recovery from cybersecurity incidents.
In a nutshell, mature organisations understand that investing in security is a business enabler that allows them to outcompete other organisations, operate more efficiently, and drastically minimise the risk of a cybersecurity incident.
In essence, it’s worthwhile.
However, this expense is not arbitrary. Far from it. There are very specific ways to understand where this investment should go.
The critical question then becomes not just how much to spend or why but how to spend it.
Proactive Security Spending Is (Always) Cheaper Than Reactive Security
So, if you are planning your cybersecurity spending for your organisation, should you focus on reactive measures, such as ransomware insurance, or on proactive measures that strengthen your security posture, like penetration testing, threat detection, and response?
If someone asked us this question, we would repeat the phrase, “Prevention is better than cure.”
Or, to rewrite it in a cybersecurity context, we might say something like, “It's much better not to be woken up at 1 AM for something that could have been prevented at 1 PM.”
That is what proactive security is in our minds - finding and fixing risks when it is convenient to do so before those risks become very inconvenient (and expensive) problems.
In a nutshell, proactive vs reactive is the difference between “No worries, we will restore from backups” and “How much did you say the ransom is?”
Comparing proactive security vs reactive security, we say that:
- Proactive security programs manage risk by systematically assessing security controls, identifying threats, and continuously re-evaluating the organisation’s security posture before an incident occurs.
- Reactive security programs address and contain an incident (such as ransomware) after it has happened.
The True Cost of Reactive Security
This struggle between spending on cybersecurity now (and reducing risk) versus saving now (and accepting cybersecurity risk, both now and later) is natural in relatively new businesses.
However, the true deferred cost of forgoing proactive cybersecurity is rarely fully accounted for.
Responding after an attack occurs can be astronomically expensive. Cyber incident costs spiral when a company has not taken proactive steps to test its environment, assure its backups, and build resilience into its operations.
One line item necessary for proactive cybersecurity is penetration testing. However, the cost of pen testing is not always necessarily as high as it might seem. Aside from testing, proactive security also requires internal time, expertise, tools, and - crucially - a culture shift.
Although proactive security cannot guarantee 100% protection against cyber incidents, it can dramatically reduce the blast radius, especially if the recommendations from the penetration testing instigate a defence-in-depth approach, where multiple security layers are implemented, assuming some may fail.
Here are just some of the costs associated with reactive security.
ICT remediation
Remediation after a cyber incident involves a combination of data recovery and incident response, but - crucially - it also entails regaining trust in your network and infrastructure.
Once you’ve been breached, your business's survival depends on regaining certainty that any damage has been fixed and that there are no lingering risks.
Your company (and your customers, clients, and investors) need complete assurance that the attacker is no longer present, that internal information assets remain under the organisation's control, and that they will not attempt to sell access to your network after extorting you. In most cases, gaining full confidence requires strategically rebuilding key parts of the infrastructure from scratch.
Attackers frequently target the same organisations multiple times or sell the network foothold they gained during the initial breach.
According to one study, 10% of companies experienced 10 or more security incidents within a single year, while 67% of organisations that suffered an attack faced another within just one year.
If an organisation fails to properly and expertly remediate after an attack, it faces dramatically higher breach risk later on.
Reputation and customer trust
Security breaches erode customer confidence, often irreparably.
Nearly half (44%) of UK consumers say they would stop spending with a business for several months after a breach, and 41% claim they would never return.
For businesses acting as third-party providers, the stakes are even higher; a breach can damage not just your direct customer relationships but also the trust your clients have with their own customers.
Downtime
Ransomware and ransom payments make headlines, but downtime from cyber incidents, including the time needed to remediate attacks, is often where the real damage occurs.
- 21% of UK SMEs that have yet to experience an attack don’t think they would have to close as a result of a cybersecurity incident, but 100% of those who have been victims of an attack said they would consider closing.
- The average duration of system downtime following a ransomware attack is 24 days.
During a ransomware attack, time is rarely on your side. Downtime becomes a pressing matter, and every moment only plays to the advantage of the perpetrators.
Other losses
Aside from the above, other costs of reactive cybersecurity may include the following:
- Permanent loss of data.
- Business IP leaking and destroying your competitive advantage.
- Productivity loss due to delays in strategic projects resulting from the need to reallocate resources to address the aftermath of the cyber incident.
- Regulatory fines from regulations like DORA, where fines are a percentage of turnover.
- Staff turnover when security talent (which is increasingly hard to come by) leaves for another job after a breach due to stress.
- Increased insurance premiums.
Proactive Security Spending Is Especially Important for Small/Medium Businesses
Proactive security provides you with the tools to manage potential incidents and protect yourself, as well as your customers and suppliers.
For small and medium-sized businesses (SMBs), the stakes around cybersecurity are existential. It’s worth noting that targeted cybercrime, like ransomware, is not exclusively an enterprise problem. In fact, 56% of ransomware attacks impact small businesses.
Enterprises can often absorb the blow of a cyber incident, but SMBs typically do not have the same resources. An estimated 60% of small businesses close within six months of a breach.
The list of organisations that failed to recover from a cyber attack grows every year. You can read about a few of these in this article about well-known UK businesses that closed following an attack.
Get Proactive with SECFORCE
Generally, we advise companies, especially those with a high reliance on IT uptime and data integrity, to aim for a slight overspend on security rather than underinvesting in it.
A small difference in spending (particularly on proactive security) can lead to significant cost differences later on.
SECFORCE can help you build a resilient, proactive security posture today.
Contact us to learn more.